Managed IT Services: Boost Productivity and Minimize Downtime
Wiki Article
How Managed IT Solutions Can Improve Your Business's Cybersecurity and Shield Delicate Information From Threats
In today's electronic landscape, the protection of sensitive data is vital for any kind of organization. Exploring this further reveals crucial understandings that can significantly influence your company's protection position.Recognizing Managed IT Solutions
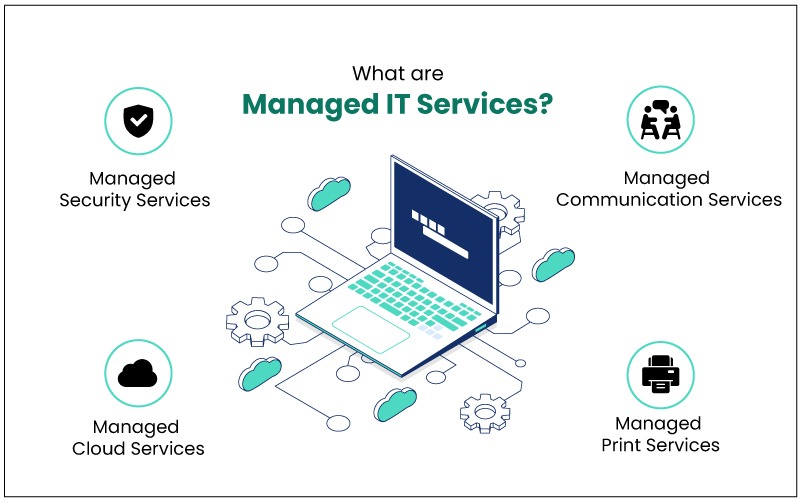
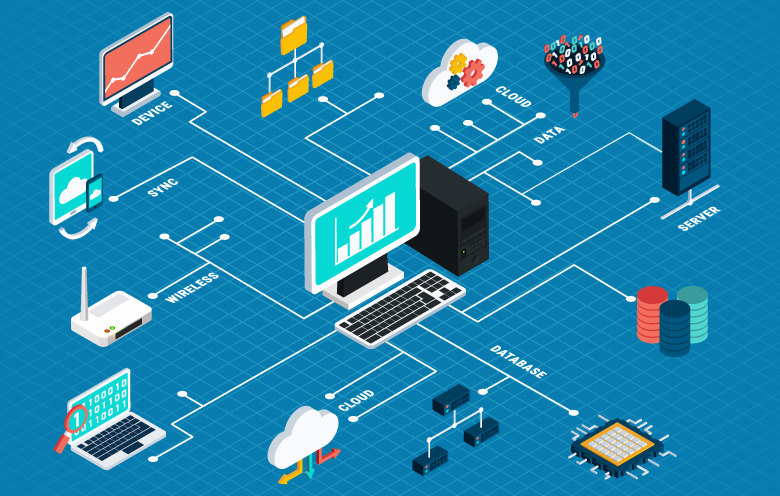
The core ideology behind managed IT services is the shift from responsive analytical to aggressive management. By outsourcing IT obligations to specialized carriers, organizations can concentrate on their core proficiencies while making sure that their technology infrastructure is efficiently maintained. This not just improves functional efficiency but additionally fosters advancement, as companies can allocate resources in the direction of tactical initiatives rather than daily IT maintenance.
In addition, managed IT solutions promote scalability, enabling business to adapt to transforming business demands without the burden of substantial internal IT financial investments. In a period where data integrity and system reliability are vital, recognizing and carrying out managed IT remedies is essential for organizations seeking to utilize innovation efficiently while guarding their operational connection.
Trick Cybersecurity Conveniences
Managed IT solutions not just enhance functional efficiency but likewise play a pivotal duty in reinforcing an organization's cybersecurity stance. Among the key advantages is the facility of a durable protection framework customized to particular business needs. Managed Cybersecurity. These services commonly consist of extensive danger analyses, enabling companies to recognize susceptabilities and address them proactively
An additional secret advantage is the assimilation of sophisticated safety and security technologies, such as firewall softwares, invasion detection systems, and file encryption methods. These devices operate in tandem to produce numerous layers of safety, making it dramatically more difficult for cybercriminals to permeate the company's defenses.
Lastly, by outsourcing IT management, business can allot sources better, permitting interior groups to focus on strategic initiatives while ensuring that cybersecurity stays a top concern. This holistic approach to cybersecurity inevitably shields sensitive data and strengthens total business honesty.
Proactive Danger Detection
A reliable cybersecurity technique depends upon positive risk discovery, which enables companies to identify and reduce prospective threats prior to they rise right into considerable occurrences. Implementing real-time monitoring solutions enables businesses to track network task constantly, providing insights into anomalies that could suggest a violation. By making use of innovative formulas and device learning, these systems can compare normal actions and prospective risks, permitting quick activity.Routine vulnerability analyses are an additional essential part of proactive danger discovery. These analyses aid companies determine weak points in their systems and applications, allowing them to remediate vulnerabilities before they can be exploited by cybercriminals. Furthermore, threat knowledge feeds play an important role in maintaining organizations informed regarding arising threats, allowing them to change their defenses appropriately.
Worker training is likewise crucial in cultivating a culture of cybersecurity click reference understanding. By equipping staff with the expertise to identify phishing attempts and other social engineering techniques, organizations can reduce the probability of successful strikes (MSPAA). Ultimately, an aggressive strategy to danger detection not just enhances a company's cybersecurity pose however likewise imparts confidence amongst stakeholders that sensitive information is being sufficiently secured against progressing hazards
Tailored Protection Techniques
Exactly how can organizations effectively protect their unique possessions in an ever-evolving cyber landscape? The response hinges on the execution of customized safety and security strategies that line up with details business needs and risk accounts. Recognizing that no two companies are alike, managed IT options offer a customized approach, ensuring that protection measures attend to the unique susceptabilities and functional demands of each entity.A customized protection method starts with a detailed threat analysis, recognizing crucial assets, potential risks, and existing vulnerabilities. This evaluation allows organizations to focus on security campaigns based upon their most pressing requirements. Following this, carrying out a multi-layered safety and security framework comes to be crucial, incorporating innovative modern technologies such as firewalls, breach detection systems, and security procedures customized to the organization's specific setting.
In addition, ongoing monitoring and regular updates are crucial components of a successful tailored method. By constantly analyzing danger intelligence and adapting safety measures, organizations can remain one step ahead of possible assaults. Taking part in staff member training and recognition programs further fortifies these methods, making sure that all employees are outfitted to recognize and react to cyber threats. With these tailored techniques, organizations can effectively improve their cybersecurity stance and secure delicate data from arising risks.
Cost-Effectiveness of Managed Provider
Organizations progressively recognize the considerable cost-effectiveness of handled IT services in today's competitive landscape. By outsourcing IT functions to specialized companies, businesses can decrease the expenses connected with maintaining an in-house IT division. This change allows companies to allot their resources a lot more successfully, concentrating on core business operations while gaining from expert cybersecurity measures.Managed IT services typically operate a membership model, offering foreseeable monthly prices that aid in budgeting and monetary preparation. This contrasts dramatically with the unforeseeable expenditures often connected with ad-hoc IT remedies or emergency situation repair work. MSP Near me. Took care of solution carriers (MSPs) offer access to advanced modern technologies and competent professionals that may otherwise be monetarily out of reach for numerous companies.
Furthermore, the aggressive nature of handled services assists mitigate the danger of pricey information violations and downtime, which can lead to significant economic losses. By purchasing handled IT services, firms not just boost their cybersecurity pose yet also recognize lasting financial savings via improved functional effectiveness and reduced danger exposure - Managed IT services. In this manner, handled IT solutions become a critical investment that sustains both monetary security and durable safety
Final Thought
In verdict, managed IT services play a pivotal role in enhancing cybersecurity for organizations by implementing personalized security methods and continuous surveillance. The aggressive detection of threats and regular assessments contribute to securing delicate data against prospective violations.Report this wiki page